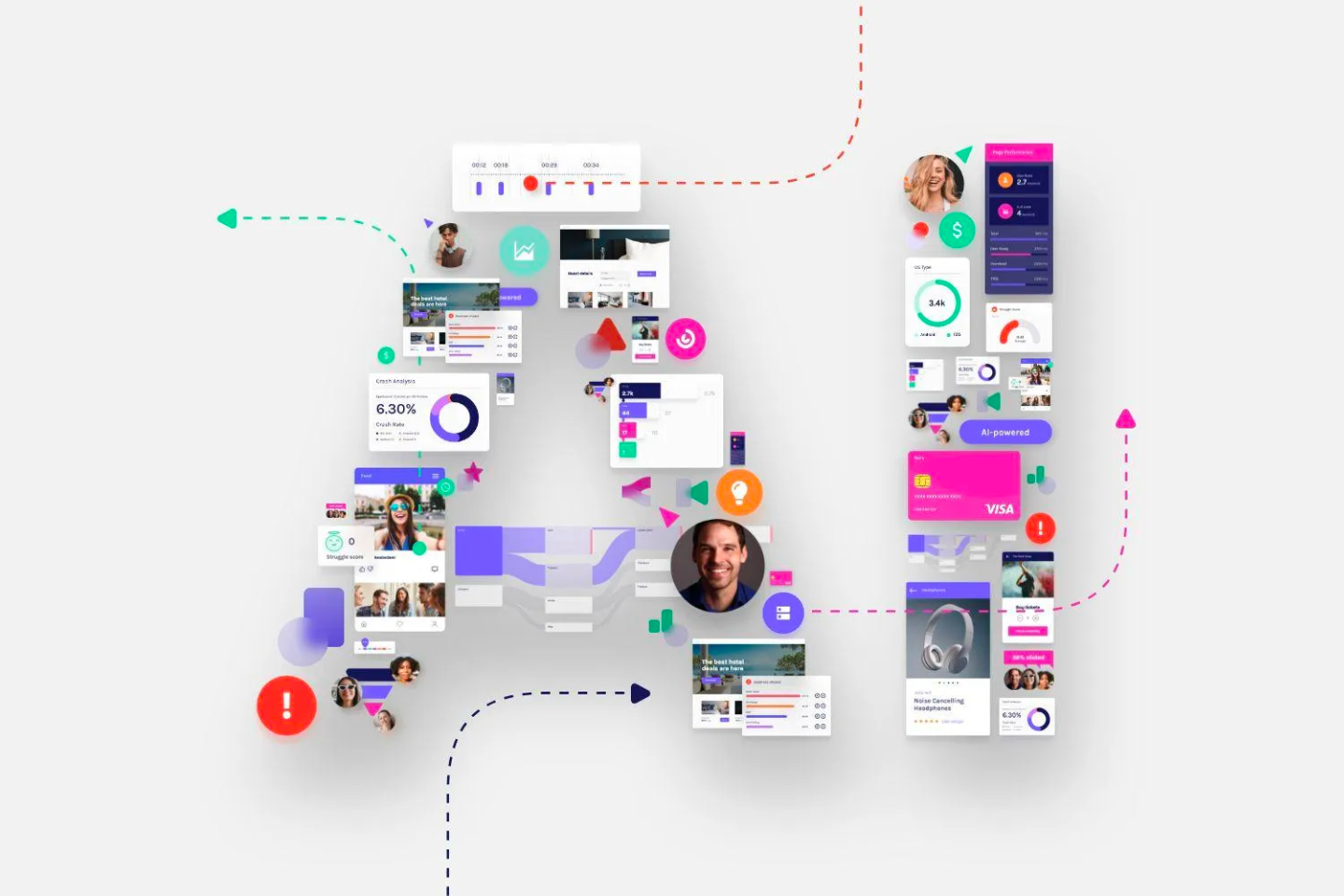
Insights
Get the latest news, views and tips from digital experience experts at Glassbox.

Compliance
Buy-now-pay-later regulations are coming to the UK. Here’s what to expect.

Customer experience
Voice of the Silent: AI is transforming customer feedback before our eyes

Mobile experience
What is App Engagement + Powerful Tips to Increase It

Customer experience
The 8 Best Customer Experience Tools in 2024
Digital experience
Autonomous CX: Generative AI is transforming digital customer journeys

Digital experience
Cyber Weekend shopping plans: Survey says digital experiences matter

Digital experience
Enhancing insurance customer experience: 10 strategies for success

Digital experience
The glaring data analytics gap in digital banking

